Hackers A Quarter Century Later
Remember the dial-up screech? The pixelated screens? It feels like a lifetime ago, and in many ways, it was. Twenty-five years ago, the world of computers and the internet was a wild frontier, and the figures who roamed it were known as hackers. But what exactly did that mean back then, and how has the landscape changed? It's a fascinating journey, filled with more than just technical jargon; it's a story about curiosity, rebellion, and the ever-evolving relationship between humans and technology.
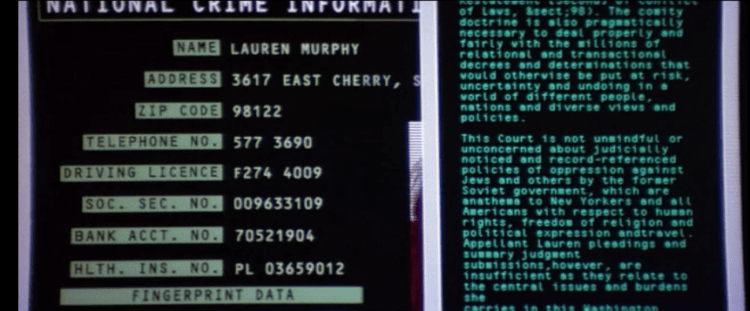
Back in the mid-to-late 90s, the term "hacker" often conjured images of shadowy figures in basements, their fingers flying across keyboards, breaching firewalls and accessing secret government databases. While that Hollywood portrayal had some kernel of truth, the reality was far more diverse. For many, hacking was about exploration. It was the joy of understanding how things worked, not to cause harm, but to push the boundaries of what was possible. Think of it as digital spelunking, navigating intricate systems to discover hidden passages and understand their architecture. These early pioneers were often driven by a profound curiosity and a desire to share their knowledge, creating communities and contributing to the nascent open-source movement.
The benefits of this early hacking culture, though sometimes controversial, were significant. These individuals often uncovered security vulnerabilities that developers had overlooked. By highlighting these weaknesses, they inadvertently forced companies and organizations to strengthen their defenses, making the internet a safer place for everyone in the long run. They were the original penetration testers, albeit without the formal titles or corporate backing. Furthermore, their tinkering and experimentation fueled innovation. Many of the technologies and protocols we take for granted today were either developed or significantly improved upon by individuals who were, by definition, hackers.
Must Read
One of the most compelling aspects of this era was the emergence of distinct hacker ethics. While not codified like laws, these principles guided the actions of many. A core tenet was the belief in the free flow of information. Hackers often saw information as a public good, meant to be shared and accessible. This clashed with the proprietary models of many software companies and government institutions. Another important principle was the rejection of unnecessary authority. Hackers often challenged established hierarchies and believed that individuals should be judged on their skills and contributions, not their titles or affiliations. This ethos fostered a sense of egalitarianism within the hacker community.
Consider the legendary figures of this time. Names like Kevin Mitnick, though often portrayed as a villain, embodied the audacious spirit of early hacking. His ability to social engineer his way into systems was legendary, highlighting the human element often overlooked in discussions of cybersecurity. Then there was the collective known as Cult of the Dead Cow (cDc), a group that not only engaged in hacking but also published influential zines and developed tools that pushed the boundaries of digital security and privacy. These weren't just individuals; they were pioneers shaping a nascent digital culture.
The tools of the trade were also quite different. Instead of sophisticated, automated exploits, much of the work involved meticulous research, understanding network protocols, and clever manipulation of existing software. A good programmer with a sharp mind and plenty of free time could potentially discover a serious vulnerability. The internet was less complex, and the security measures were, by today's standards, rudimentary. This made the act of "breaking in" more about ingenuity and persistence than brute force.

Looking back, it's easy to romanticize this era. The internet was still a novelty for many, and the concept of digital identity and privacy was far less developed. This created a unique environment where experimentation could flourish with fewer immediate consequences, at least for some. However, it's crucial to remember that not all hacking was benign. Even in those early days, there were individuals who used their skills for malicious purposes, stealing data, causing disruption, and engaging in financial fraud. The line between ethical exploration and criminal activity was, and remains, a delicate one.
Twenty-five years on, the landscape has transformed dramatically. The internet is ubiquitous, security is a multi-billion dollar industry, and the term "hacker" is often synonymous with cybercriminal. However, the spirit of curiosity and the drive to understand and improve systems still exists. It's just evolved. Today, we have ethical hackers, bug bounty hunters, and cybersecurity professionals who dedicate their careers to finding and fixing vulnerabilities. The playful, exploratory side of hacking has found a more legitimate, albeit often less glamorous, outlet. The lessons learned from those early days continue to inform our understanding of digital security and the ongoing dance between those who build and those who seek to deconstruct.







